Software is not a product. Unlike that chair you’re on, or that phone you have, software is useless outside the platform it’s built for.
Not only that, software is time-bound. That version of software you have on your phone needs to keep up with your OS version, or else will it break. It is slave to the relentless march of technology.
Thus, software is really a service. It has to be built but more importantly, it has to be maintained to be truly useful and fruitful. Sure you can use it for a couple of years, maybe, but when the platform it’s on gets abandoned or one of its more important features breaks, people will quickly flock to another alternative.
But who can maintain software? It’s certainly not your tech support team and definitely not the customer service people. You need software engineers to keep software serving as it should.
So if you are in the business of software, you need to do a few things to make sure it keeps running:
- Retain developers. Keep them motivated and productive. It’s less about perks and more about growth. Build a culture where developers are valued and heard.
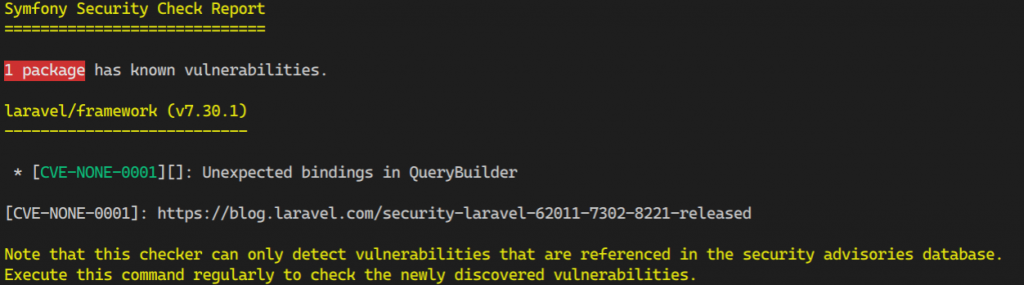
- Focus on code quality. Make a case to stakeholders that this is practical and lowers costs even if it can be difficult at the start. This will also lead to happier devs since they spend less time fixing and more time building.
- Make sure knowledge about the inner workings of your software lives in more than one developer. This is not only pragmatic in the business sense, but also makes sure that at least two people can work on bugs and features. There’s a reason the buddy system works in large institutions like the police.
- When developers leave (and they will, it’s as sure as gravity), there needs to be a process in place for them to transfer their knowledge about your software. Best if this is actually part of their routines, but if not, having a knowledge transfer process is critical.
- Keep hiring. The cycle of developers leaving also benefits you since there are other developers leaving other companies you can snatch up as well.